Research Experience for Teachers (2015-2016)
Securing Cyberspace
 |
||||||
|
||||||
|
Pre/Post Test: Pre-Test Post-Test |
||||||
|
The Big Idea (including global relevance) Cybersecurity |
|
Essential Questions How do you encrypt/decrypt data? |
|
The Hook
|
|
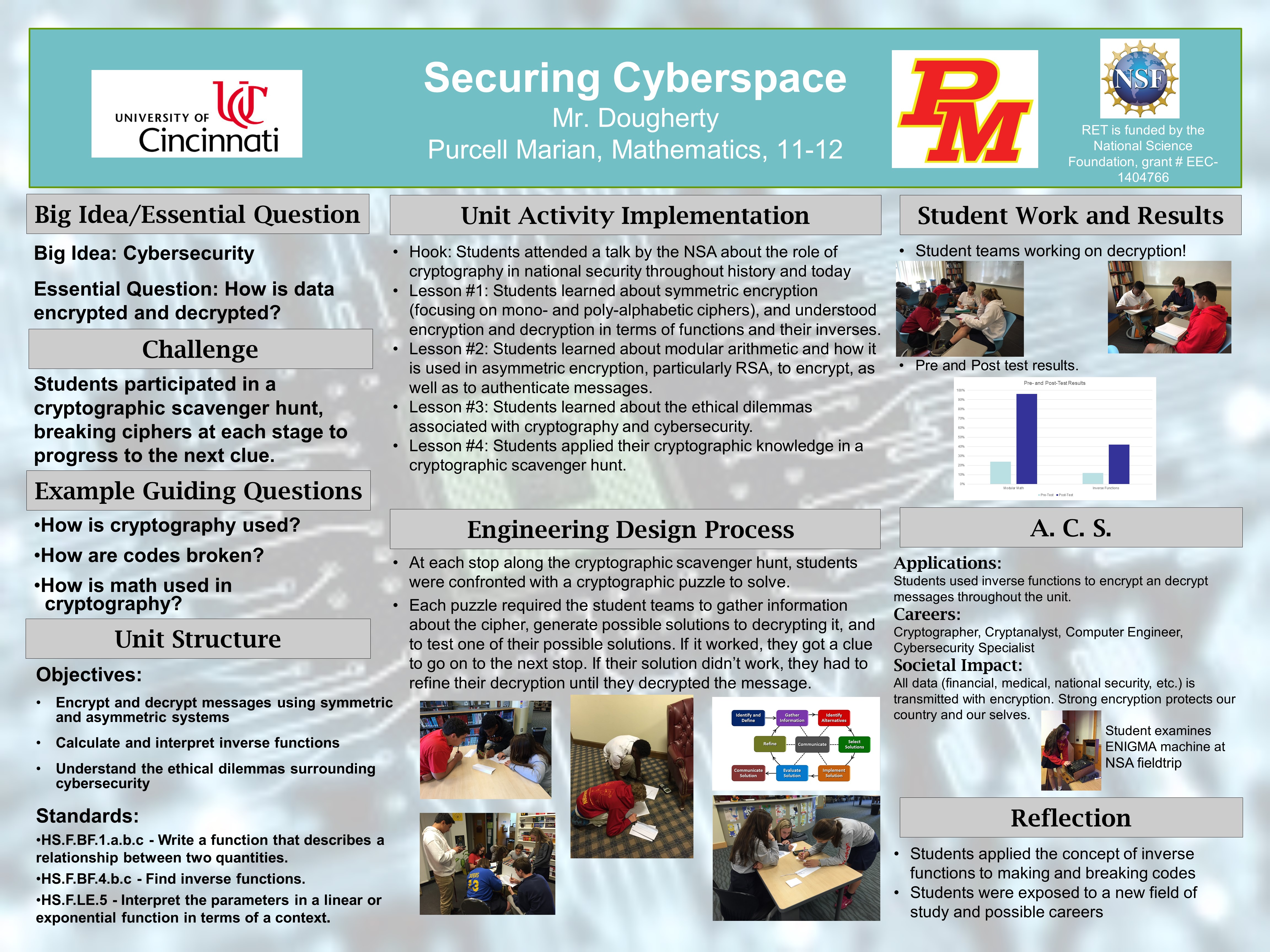
The Challenge Students will apply their encryption and decryption knowledge to break codes at stations in a scavenger hunt. Each successfully broken code will give them the clue to the next stop on the scavenger hunt. |
|
Guiding Questions
|
ACS (Real world applications; career connections; societal impact)
Students will be engaged in a scaled-down version of what cyber security experts go through on a daily basis.
When cyber security fails, the societal impact is high in terms of lost financial resources or compromised personal data. Studying how to protect against the cyber security breaches thus has high societal impact.
I’ll use a guest speaker to introduce students to careers in cyber security and computer science in general.
Misconceptions
- Students believe that the information they transmit via telephones and computers is secure.
Unit Lessons and Activities
- Lesson 1: Introduction to Cryptography and the Mathematics of Cryptographic Systems The first lesson will introduce the big idea of cybersecurity and “hook” the students into the unit by showing them how devastating a lack of cybersecurity can be such as with the Stuxnet virus. Students will be introduced to monoalphabetic ciphers through the Caesar cipher, and they will learn how to break them using frequency analysis. Students will also learn about the difference between symmetric and asymmetric encryption systems, and have an opportunity to encrypt and decrypt using the popular RSA algorithm. Throughout this first lesson, students will be interpreting ciphers as kinds of functions, and learning decryption as a kind of inverse function.
- Activity 1: Introduction (3 days)
- Activity 2: Public Key (Asymmetric) Cryptography (4 days)
- Lesson 2: Cryptography and Ethics The second lesson will introduce students to some of the ethical dilemmas (both historical and current) related to cryptography and cybersecurity. Students will have the opportunity to debate various dilemmas and establish criteria for considering the ethics of a situation. Students will review and condense their knowledge of cryptography and cryptographic systems. Finally, students will participate in a multi-day war simulation game in which they will be using the cryptography from the unit to communicate securely with their team to win the game.
- Activity 3: Ethical Considerations and Review (2 day)
- Activity 4: Cryptographic Scavenger Hunt (1 days)
- Evidence of CBL: Activity 1, 2, 4
- Evidence of EDP: Activity 1, 4
Additional Resources
