Research Experience for Teachers (2015-2016)
The Mathematics of Cyber-Security and Cryptography
 |
||||||
|
||||||
|
Pre/Post Test: |
||||||
|
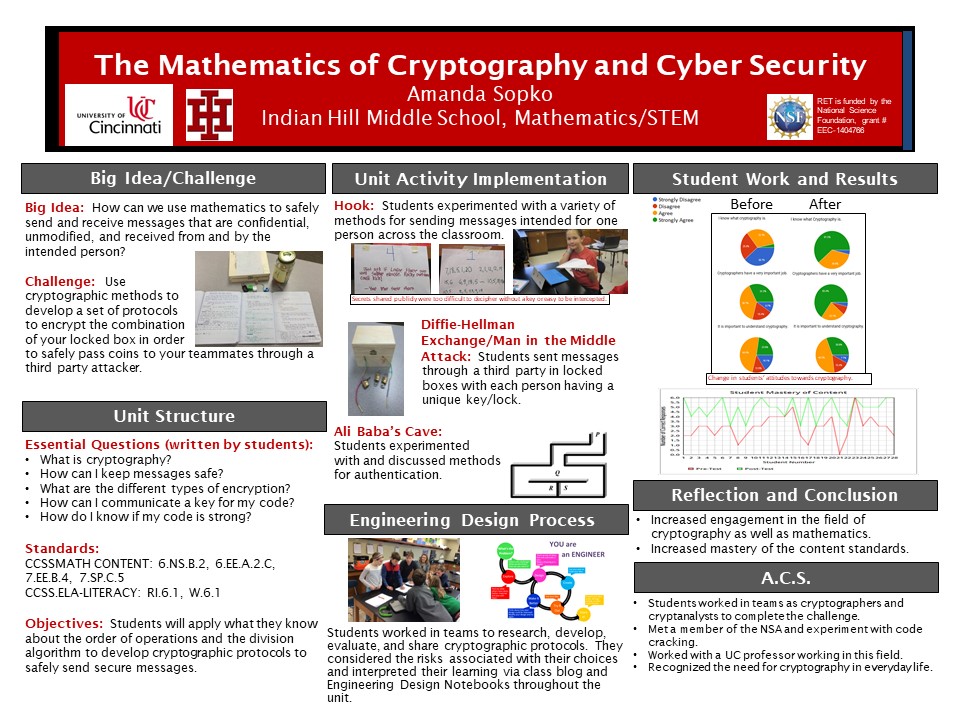
The Big Idea (including global relevance) How secure is the data you send via text messages, email, and private chats with friends? In this unit, students will use mathematics to examine the historical and personal significance of cryptology. Students will evaluate messages sent over networks through secret and public keys and use this information to send a message through a third party without divulging the information in the message. |
|
Essential Questions
|
|
The Hook
|
|
The Challenge Secret Agent: Design a message to pass from one secret agent to the other through a third party. |
|
Guiding Questions
|
ACS (Real world applications; career connections; societal impact)
Students send digital data across networks multiple times on a daily basis. It is important to discuss the importance and methods of keeping this information safe and secret from a third party.
There have been multiple security breaches that have changed the course of history and greatly reduced the length of wars. These breaches have driven the systems we have in place today to keep all data including short text messages we share with peers out of public view. These changes have also provided a need for creating and enforcing strict laws for the sharing of data over a network. With these new technologies, there is also a great need for the direct instruction of ethical practices.
Students will be introduced to the field of cryptography. They will be exposed to professionals in the NSA.
Misconceptions
- Data sent via email or text message are protected by passwords and can not be seen by anyone other than the intended recipient.
Unit Lessons and Activities
- Lesson 1: What is Cryptography and why is it important? This lesson introduces students to cryptography through the hook and a lesson on the history of cryptography. Next, the students explore various ciphers through hands-on and virtual activities. Finally, the students participate in a series of hands-on activities to discover and explore the Diffie-Hellman and RSA exchanges followed by using the algorithm to complete exchanges abstractly.
- Activity 1: Sharing Messages - 3 days
- Activity 2: Secret Key vs Public Key System - 4 days
- Lesson 2: How do I keep my information safe? The second lesson in this unit focuses on cyber attacks and protecting data. The students use the algorithms they learned in the previous task to attack and prevent attacks. The second activity in this lesson has the unit challenge. During the challenge, the students will attempt to send coins to their teammates without interception from other teams. Finally, the students will participate in an activity on ethical use of the information in this unit.
- Activity 3: Cyber Attacks - 1 day
- Activity 4: Collecting coins challenge - 4 days
- Activity 5: Ethics - 1 day
- Evidence of CBL: L2 A4
- Evidence of EDP: L1 A1, L1 A2, L1 A3, L1 A4
Additional Resources
